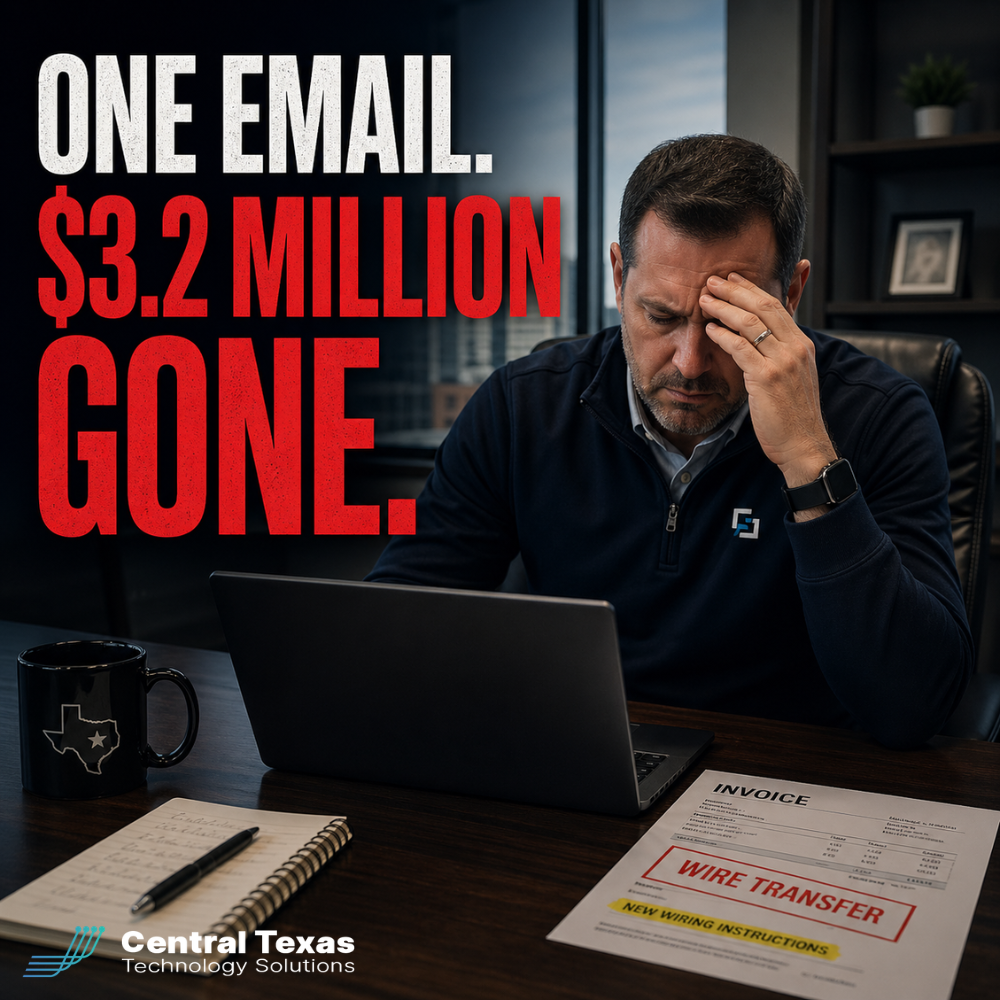
 It does not take a sophisticated cyberattack to lose millions.
It does not take a sophisticated cyberattack to lose millions.
It takes one email.
A school district recently lost $3.2 million after processing what appeared to be a legitimate invoice. The email thread was real. The vendor was real. The project was real.
The wiring instructions were not.
This type of attack is called Business Email Compromise, and it is one of the most dangerous threats facing organizations today.
If you are a CEO, CFO, or business owner in Central Texas, this is not a hypothetical risk. It is happening every day to organizations just like yours.
The Real Cost of Ignoring This Risk
Most business leaders assume cybersecurity threats look like ransomware or viruses.
That assumption is exactly what attackers rely on.
Business Email Compromise works because it looks normal.
No alarms
No suspicious links
No obvious warning signs
Just a familiar conversation with one critical change.
If your team processes payments based on email instructions alone, you are exposed.
The consequences go far beyond the financial loss:
Loss of trust with vendors
Internal accountability issues
Potential legal and insurance complications
Operational disruption
And in many cases, the money is never recovered.
Why Most Businesses Are Vulnerable
This is not a technology problem. It is a process problem.
Even companies with strong IT systems fall victim because:
There is no verification process for payment changes
Employees are not trained to recognize subtle fraud tactics
Email systems are not monitored for account compromise
Approval workflows are inconsistent
Attackers do not break systems. They manipulate people and processes.
That is why traditional IT support alone is not enough.
How CTTS Helps You Eliminate This Risk
At CTTS, we work with business leaders across Austin, Georgetown, Round Rock, and surrounding Central Texas communities to close these gaps.
We focus on practical, business-level protection, not just technical controls.
Our approach includes:
Proactive email security monitoring
Advanced threat detection and response
Employee training based on real-world scenarios
Clear, enforceable financial verification processes
We help your team move from reactive to prepared.
Because prevention is always less expensive than recovery.
4 Practical Steps Every Business Should Take Today
You do not need a complete overhaul to reduce your risk. Start with these fundamentals.
1. Require Verbal Verification for Payment Changes
Any request to change banking or payment details should be verified with a known, trusted phone number. Not one provided in the email.
2. Implement Dual Approval for Wire Transfers
No single employee should have the authority to approve large financial transactions alone.
3. Train Your Team on Real Scenarios
Generic cybersecurity training is not enough. Your team needs to see examples of real email compromise attacks.
4. Secure Your Email Environment
Multi-factor authentication, monitoring, and advanced filtering should be standard.
5. Document and Enforce a Payment Process
Consistency is key. Every employee should follow the same process every time.
What Success Looks Like
When these controls are in place, something powerful happens.
Suspicious requests get flagged immediately
Employees pause instead of reacting
Fraud attempts fail before money moves
Your business operates with confidence instead of uncertainty.
That is what strong IT support and cybersecurity should deliver.
Final Thought
The most dangerous cyberattacks are not the loud ones.
They are the quiet ones that look like business as usual.
If your current process relies on trusting email alone, it is time to take a closer look.
Schedule a Free Strategy Session
If you want to understand where your risks are and how to fix them, we can help.
Schedule a free strategy session with CTTS and get a clear plan to protect your business.
Frequently Asked Questions
What is Business Email Compromise?
It is a cyberattack where criminals gain access to or impersonate email accounts to trick businesses into sending money or sensitive information.
Can this happen even if we use Microsoft 365?
Yes. While platforms like Microsoft 365 have strong security features, they must be properly configured and supported with additional safeguards and processes.
How quickly can funds be recovered after a wire fraud incident?
Recovery depends on how quickly the fraud is reported. Immediate action increases the chances, but recovery is never guaranteed.
Contact CTTS today for IT support and managed services in Austin, TX. Let us handle your IT so you can focus on growing your business. Visit CTTSonline.com or call us at (512) 388-5559 to get started!
