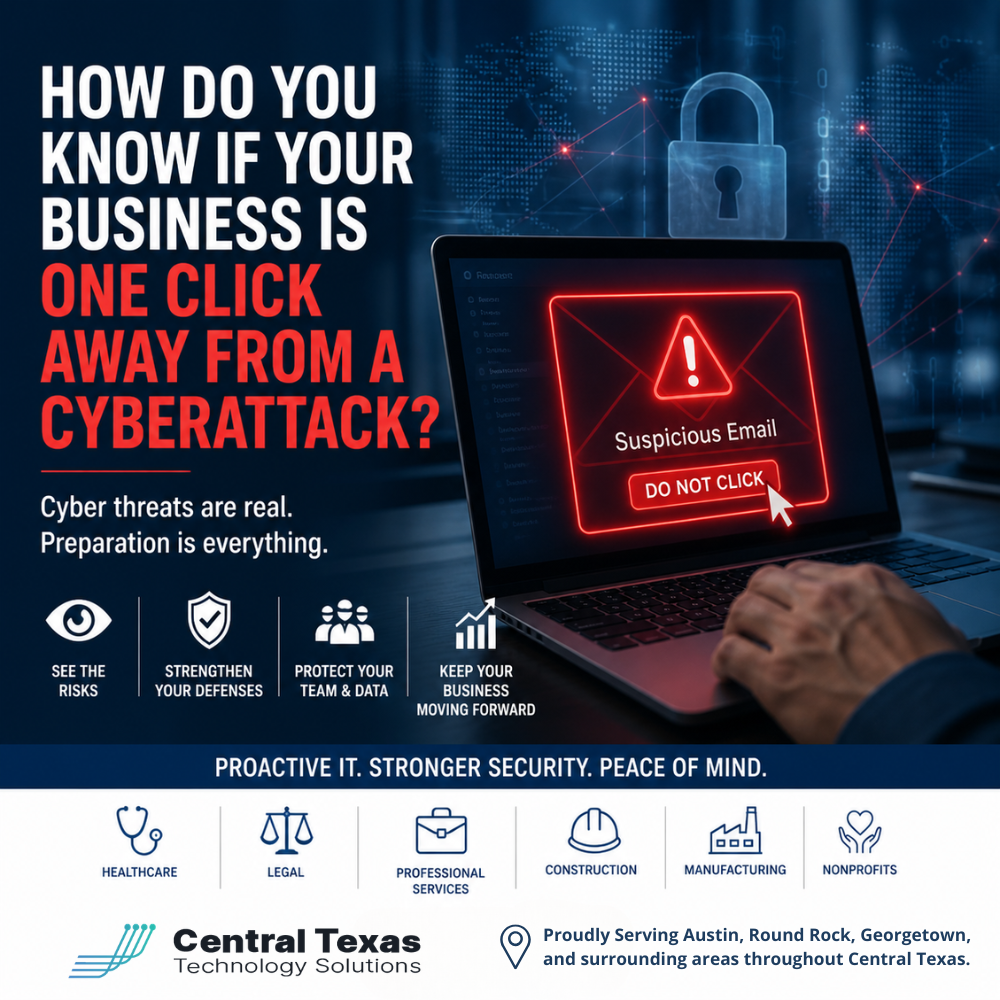
 Every day, your team clicks links, opens emails, logs into systems, and shares files. It feels routine. It feels safe.
Every day, your team clicks links, opens emails, logs into systems, and shares files. It feels routine. It feels safe.
But for many businesses in Austin and across Central Texas, that single click is where a cyberattack begins.
Whether you lead a healthcare practice handling patient data, a legal firm managing confidential cases, a professional services company coordinating client work, a construction business sharing project files, a manufacturing company running production systems, or a nonprofit protecting donor information, the risk is the same.
The question is not if your team is clicking. It is whether those clicks are protected.
The Hidden Risk Behind Everyday Clicks
Cyberattacks no longer rely on obvious scams. Today’s threats are designed to look legitimate.
A message appears to come from Microsoft 365.
A vendor sends what looks like a normal invoice.
A team member receives a shared document request.
Everything feels familiar.
But one click can:
- Hand over login credentials
- Install hidden malware
- Give attackers access to your systems
- Expose sensitive client or patient data
For businesses in Austin, Round Rock, Georgetown, and Cedar Park, this is not a rare event. It is happening every day, often without immediate detection.
Why Most Businesses Don't See It Coming
Many business leaders assume they are protected because they have basic security tools in place.
Antivirus is installed.
Passwords are required.
Maybe even multi-factor authentication is enabled.
But cybercriminals have adapted.
They target people, not just systems.
That means:
- A well-crafted phishing email can bypass technical defenses
- Employees may unknowingly approve malicious login requests
- Vendors and third-party tools can introduce risk
- Old or unused accounts can become entry points
In industries like healthcare and legal, where compliance matters, or construction and manufacturing, where downtime impacts operations, the consequences can be severe.
And nonprofits, often operating with limited IT resources, are frequent targets because attackers assume defenses are weaker.
Signs Your Business May Be One Click Away
Most cyberattacks leave warning signs before something serious happens. The challenge is knowing what to look for.
Here are a few red flags:
- Employees frequently receive unexpected login prompts
- You rely heavily on email for file sharing without verification steps
- There is no formal cybersecurity training for your team
- Vendors have access to your systems without regular review
- You are unsure who has access to what across your network
- Security tools are in place, but no one is actively monitoring them
If any of these sound familiar, your business may be closer to a cyberattack than you think.
The Real Cost of Ignoring the Risk
It is easy to assume nothing will happen until it does.
But one successful attack can lead to:
- Business downtime that stops operations
- Lost revenue from interrupted services
- Damage to your reputation and client trust
- Regulatory penalties for data exposure
- Expensive recovery efforts
For a healthcare provider, that could mean compromised patient records.
For a legal firm, it could expose sensitive case data.
For a construction company, it could delay projects and payments.
For a manufacturer, it could halt production lines.
For a nonprofit, it could impact donor confidence and funding.
The risk is not just technical. It is business-critical.
What Protection Actually Looks Like
The solution is not more tools. It is a better strategy.
Strong cybersecurity starts with visibility and control.
That includes:
- Proactive monitoring that detects unusual activity early
- Security awareness training that teaches employees how to spot threats
- Controlled access to systems based on roles and responsibilities
- Regular reviews of vendor and third-party access
- Advanced email protection that filters and flags suspicious messages
- A clear incident response plan so your team knows what to do
Businesses in Austin, Georgetown, Round Rock, and Temple that take this approach are not just reacting to threats. They are preventing them.
Why a Proactive IT Partner Makes the Difference
Most internal teams do not have the time or resources to stay ahead of evolving threats.
That is where CTTS comes in.
CTTS helps businesses across healthcare, legal, professional services, construction, manufacturing, and nonprofits move from reactive IT support to proactive protection.
Instead of waiting for something to break, CTTS:
- Monitors your systems continuously
- Identifies risks before they become incidents
- Aligns your security strategy with your business goals
- Guides your team with clear, practical recommendations
You are not left guessing. You have a partner who sees what is coming and helps you stay ahead of it.
Take the Next Step Before the Next Click
If you are not sure where your risks are, that is the first problem to solve.
You do not need to overhaul everything overnight. You just need clarity.
Start with a conversation.
CTTS can assess your current environment, identify where you are exposed, and show you how to reduce your risk in a practical, manageable way.
Schedule a consultation today and find out if your business is one click away from a cyberattack.
Frequently Asked Questions
How do most cyberattacks start?
Most cyberattacks begin with phishing emails or compromised credentials. A user clicks a link, enters login information, or downloads a file that gives attackers access.
Is multi-factor authentication enough to stop cyberattacks?
Multi-factor authentication is important, but it is not enough on its own. Attackers now use techniques that can bypass or trick users into approving access.
How often should businesses review their cybersecurity setup?
At a minimum, businesses should review their cybersecurity strategy annually. However, ongoing monitoring and regular updates are critical to staying protected.
Contact CTTS today for IT support and managed services in Austin, TX. Let us handle your IT so you can focus on growing your business. Visit CTTSonline.com or call us at (512) 388-5559 to get started!
Explore these expert insights before making your next IT decision:
What Happens When Businesses Wait Too Long to Fix Their IT Problems?
The Most Common IT Support Mistakes Austin Businesses Make
How Poor IT Network Support Puts Your Business at Risk
Why Ransomware Attacks Target Small and Mid Sized Texas Businesses
